How to verify MD5, SHA256 checksum of a cryptocurrency wallet / software
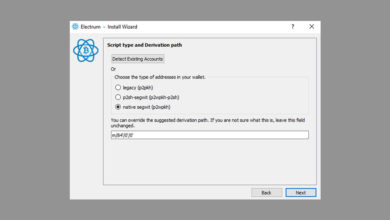
MD5 and SHA256 checksum: Recently one of our user asked “In the Github page I do see several Windows 64 files; a .exe file, a .md5sum file and a .sha256sum file; which one should I download?” We told them to download the .exe file or the .zip file which is larger in size. The ones that are bigger in file size are the actual wallet files and the rest are all just checksums. Alright! But what are all these MD5sum and SHA256sum files and why do the developers put these files next to the downloadable files?
MD5 and SHA256 hash
SHA256sum and MD5sum are programs that implement SHA256 and MD5 hash algorithms respectively which is mainly used to confirm the file integrity and authenticity.
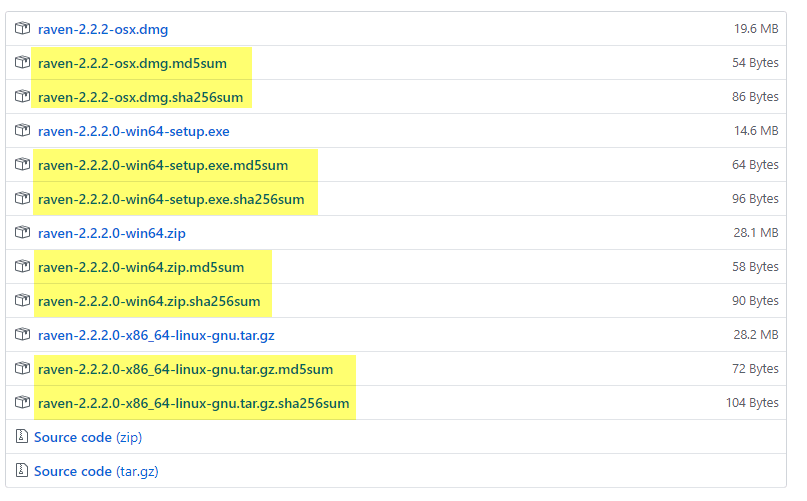
Both MD5 and SHA256 are two different hashing algorithms and it’s up to the developers to decide on which hash to provide on the download page. As you can see above; the developers of the Ravencoin project have provided both MD5 hash and SHA256 hash for verifying the wallet download file. But this is not something that you’ll find in the download page of every other cryptocurrency wallet software’s. Due to security flaws in MD5 algorithm most developers won’t provide MD5 hash. Currently only SHA256 hash values are being used widely.
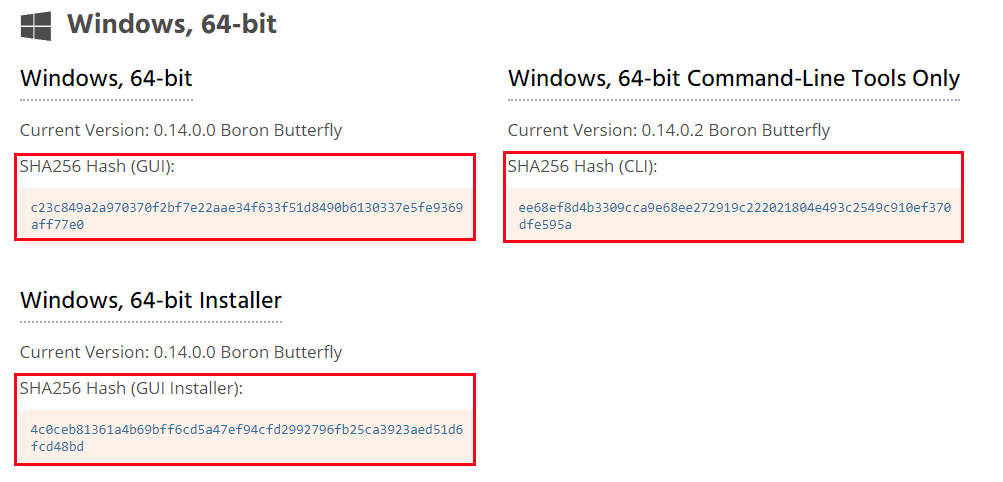
In Monero website you might have noticed SHA256 hashes listed alongside the software.
While some developers create and distribute hashes alongside with each software release; some developers digitally sign each new version of the installer package with the official developer’s signature.
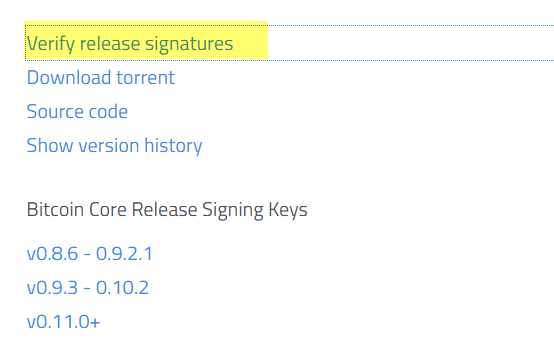
In Bitcoin core you’ll find something called release signatures or in other words they are also called release hashes. They are ASC file which usually contains SHA256 hash and a PGP signature.
Just download the file and open it using Notepad or preferably in Notepad++. You’ll see a random string of letters and numbers similar to this.
-----BEGIN PGP SIGNED MESSAGE----- Hash: SHA256 5659c436ca92eed8ef42d5b2d162ff6283feba220748f9a373a5a53968975e34 bitcoin-0.17.1-aarch64-linux-gnu.tar.gz aab3c1fb92e47734fadded1d3f9ccf0ac5a59e3cdc28c43a52fcab9f0cb395bc bitcoin-0.17.1-arm-linux-gnueabihf.tar.gz b1e1dcf8265521fef9021a9d49d8661833e3f844ca9a410a9dd12a617553dda1 bitcoin-0.17.1-i686-pc-linux-gnu.tar.gz 6aa567381b95a20ac96b0b949701b04729a0c5796c320481bfa1db22da25efdb bitcoin-0.17.1-osx64.tar.gz e3d785d800b71d277959d15b2c2b33d44dd72c1288e559928a40488dd935c949 bitcoin-0.17.1-osx.dmg 3e564fb5cf832f39e930e19c83ea53e09cfe6f93a663294ed83a32e194bda42a bitcoin-0.17.1.tar.gz e9245e682126ef9fa4998eabbbdd1c3959df811dc10df60be626a5e5ffba9b78 bitcoin-0.17.1-win32-setup.exe 6464aa2d338f3697950613bb88124e58d6ce78ead5e9ecacb5ba79d1e86a4e30 bitcoin-0.17.1-win32.zip fa1e80c5e4ecc705549a8061e5e7e0aa6b2d26967f99681b5989d9bd938d8467 bitcoin-0.17.1-win64-setup.exe 1abbe6aa170ce7d8263d262f8cb0ae2a5bb3993aacd2f0c7e5316ae595fe81d7 bitcoin-0.17.1-win64.zip 53ffca45809127c9ba33ce0080558634101ec49de5224b2998c489b6d0fc2b17 bitcoin-0.17.1-x86_64-linux-gnu.tar.gz -----BEGIN PGP SIGNATURE----- Version: GnuPG v1.4.11 (GNU/Linux) iQIcBAEBCAAGBQJcIeQ5AAoJEJDIAZ42wulk0NoQAIunIBT06bd2IhhxV/48NUvf sgTto4qYrKuX5Vkn+kfGuMBvNpmILi5CiVtnucWo7fKM6k5IPMyBQuE9iDVDzT9i YemA9Au8Xy2aIGmVriuQoXxk8b17wAMS9uw362A3nXCz3kA+BWMDuMfBp3P3NPM/ PeOg6n04Q7seO/zNdT5i/ysaFB/XA8szrQxCRukSrXeGMUpv79UbcWOu3+nfGit9 yYo/F2yO57Yacv597rKILlg29QxEVTqa5+slMdwuU7NP5AdAcQV4EtFqoCOqM7C7 JL/zZWYnTywK3l0hOuCBJiY86izutWME5xgm7Eh3ORj+K6ZYT4iXw2JIkTdumeuS X0WDE3ShH4rb35IaQX75FJLp5R7hLTXiNgng7b8Xhy/62bJ75Ob4HVVSLG1Lkhps vtml10br+78qXiofzk8zaAW6KaG7G9nbBa0hfDjUEsYzA6P5iWA+53ykupc82HNa ZT2gk+wWhNhZOd/ANheriM0eqm/ZlK7oydYRRtf9Tamk+XJgREU1x8cWlMZcCPEE uIUzb7/REvYSjwcwArYLCq/eFPfjQe7jcG2WexnpxxkKJBvu2v4zVw9LLUPll094 BAmfk34iJKhN2cGVhvjO0Q9GKk0B2HzvhD5xn1Hnlp+NbXVNbKonYvkB71D3GY4W t/eRyv7Erfi4dhHf+8oQ =UEoM -----END PGP SIGNATURE-----
These are cryptographic hash and these information are provided for the users to verify the file integrity. Cryptocurrency developers and often websites indicate users to verify the authenticity of the download file before using it. However most users do not care or not sure what to do with these information. So we decided to make a topic on this. Here in this beginners guide we’ll show you how to validate checksums (only SHA256 hash and MD5 hash and not the PGP signatures).
But wait!? Anyways I’m downloading the wallet from the official source so why should I verify that my wallet download is authentic? Also what is checksum and how does verifying checksum help?
What does checksum mean and how it works?
As the word implies “checksum” means check something or check the sum. The checksum string is a random hash value that is created from scanning the contents of the program. Developers often create and distribute these checksum strings at the release of each wallet software. Why?
One of the main issue and top concern among cryptocurrency users is security and trust. When downloading files online we can’t be 100% sure that the file is original; even if you’ve downloaded from the official source. There are chances where a 3rd party can modify file in transit or hack the server where the file is being hosted and replace it with a malicious version. But here is the thing: If any third party tries to alter the software, even 1 bit then the output hash value of the checksum string will be completely different from the one provided by the developer. By providing checksums users can verify and make sure that they’ve downloaded the legitimate copy of the wallet software published by the developer.
One of the standardized ways of determining whether if a program file has been modified from its original state or not is by looking at its hash value (verifying checksum). Simply calculate checksum of the software and compare it with the one shared by the developer. If it matches then the file is authentic; if not then either the download is corrupt or it has been tampered.
Verifying the hash of the download files before using them is generally a good security practice. If you are not sure how to verify checksum then follow the guide below.
How to verify checksum (MD5 / SHA256) in Windows, Linux & Mac?
To explain things better; here in this tutorial we’ll be verifying the checksum of Monero GUI wallet to ensure that it is indeed the correct file. You can use the same steps below to verify checksum of any cryptocurrency wallet download files. For verifying Bitcoin software refer to this guide.
First download the wallet file or software for which you wish to validate checksum.
Windows:
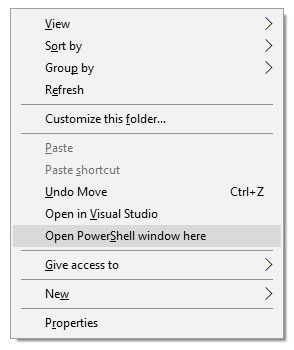
Navigate to the downloads folder or to the location where you have downloaded the file. Now SHIFT + right click and then click open PowerShell window here which will open the command prompt.
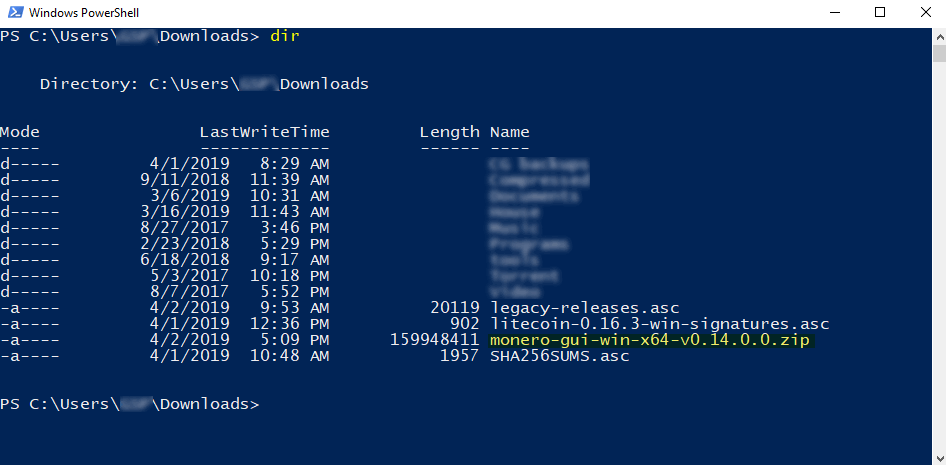
Type “dir” without quotes and hit enter which will display the list of all files and folders within that directory.
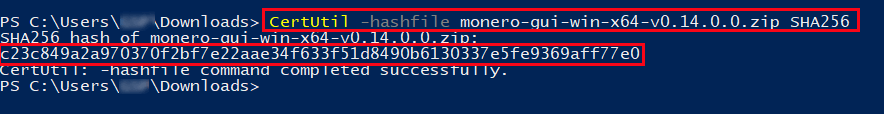
Now highlight the file for which you’d like to verify checksum and then click CTRL + C to copy. Then enter the following command accordingly to verify MD5 hash and SHA256 hash.
MD5: CertUtil -hashfile filename MD5
SHA256: CertUtil -hashfile filename SHA256 (Example: CertUtil -hashfile monero-gui-win-x64-v0.14.0.0.zip SHA256)
Once done, hit enter. The command window will now display the hash value of the file depending on the hash algorithm you chose. If you chose SHA256 algorithm then it will display SHA256 hash. If you chose MD5 algorithm then it will display MD5 hash.
Linux:
The procedure is same for Linux and Mac, except you don’t open command prompt here. Instead we’ll be using the terminal window.
SHA256: sha256sum <path>/<filename> | MD5: md5sum <path>/<filename>
Mac: shasum -a 256 filename
Now compare the hash value generated in the command window to the hash value distributed by the wallet developer. Just copy them and verify it. If you got the right sequence then wallet file is legit. You can go ahead and install it now. However if they do not match then do not install the file. Either the download file is corrupt or it could be malicious. Be sure to delete the file, download it again and then validate checksum to make sure the validation result is positive.
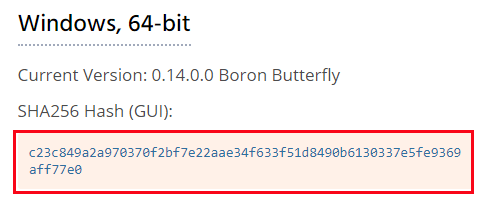
Note: Developers often post hash values of the downloadable wallet installers on their website and on Github. What you need to note is that each hash value is unique and it differs for each and every version. So it is important that you verify the integrity of the wallet software each time you download a new version. This way you can be sure that the wallet software you are using is a genuine copy.
Digital signatures: GPG / PGP signatures
But wait!? What if the website is compromised and the hacker managed to alter both the wallet file and the hash values accordingly? It happens and this is why most developers won’t publish both hash values and the binaries in the same location. Moreover SHA256 and MD5 checksum are something which people used in the early days. Currently PGP is being used widely which is a more secure way of verifying file integrity. In addition to SHA256 hash some developers publish PGP signed hashes of the wallet installer. Some on the other hand only provide GPG signatures.
For example: Learn how to verify Electrum wallet signatures.