How to check hash (checksum) / verify PGP signature of Ledger Live app
Hardware wallets, despite providing the most secure storage solution many users still lose their coins. Particularly newbies and its mainly because of their negligence. They fall for the most obvious scams.
The very first step that you need to take in protecting your crypto is to stay away from phishing scams.
After the data breach on the Ledger website there are regular phishing campaigns going on over Twitter / YouTube, SMS and Email. There are many reports of users falling victim to these phishing attacks.
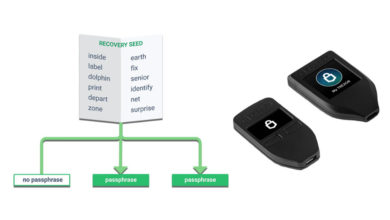
Remember that the hackers main target is your recovery seed phrase. Most of the phishing techniques are focused on obtaining your recovery phrase.
Make sure to keep your 24 word recover phrase safe, private and completely offline. Never ever share your backup recovery phrase with anyone. Also do not keep a digital copy. Do not enter this information on your computer or smart phone or on the web. Do not take pics and do not print. You should only write them in a piece of paper or on a metal plate. You’ll only need this information in future to recover your funds in case if your device is lost or broken.
You should only enter the recovery phrase on a legitimate hardware wallet. Here is how you can check if your Ledger device is genuine:
https://support.ledger.com/article/13692454787613-zd
Aside from verifying the authenticity of your device you also need to ensure that you are running a genuine Ledger Live application. You can do so by checking the hash / verifying signature of Ledger Live.
Here in this beginners guide let’s see how to check hash (checksum) / verify PGP signature of Ledger Live.
Why to verify Ledger Live?
Some might argue that verifying the authenticity of Ledger Live doesn’t matter because the private keys are securely stored on the device. It’s True. The whole point of hardware wallet is that they keep your coins safe even though when operated on a compromised environment. But still you are highly susceptible to phishing attacks.
For example let’s say you downloaded Ledger Live from the email link which you recently received. You may not know that its a fake wallet application that is tampered by a malicious 3rd party until you verify the software. Now just by installing a malicious app hackers cannot steel your funds from your hardware wallet. But this compromised software can trick you in many ways.
1. A fake wallet application might ask the details of your 24-word recovery phrase. Many users know that the recovery phrase should not be entered on anything else than the Ledger device. But as we said new users may not be aware of this and they would be fooled by this technique.
Remember that Ledger Live software will never ask for your recovery phrase or passphrase. If the application is asking for your recovery phrase then it is obvious that it is a malicious app designed to steal your coins.
2. A compromised ledger live application will have backdoor and they could generate vanity address mimicking your destination address.
Remember that before you confirm any transaction do check the destination address on your Ledger device.
To protect against such malicious modifications make sure that you;
- Always download Ledger live from the official website.
- Verify the Ledger live app before installing.
Verifying software is a basic security step
Hardware wallet is an excellent start. But still you need to take all precautions to protect your cryptocurrencies against malicious practices.
Not just wallet application but this should be done to any software that you install on your computer especially since you are dealing with crypto. You need to be aware of its origin and need to verify the software to ensure it is authentic.
This is a standard practice and as a user of cryptocurrency you should keep this as a general rule. This will greatly protect you from all sorts of malware.
Previously we’ve explained how to check MD5 / SHA256 hash of a wallet. Also we’ve a made a tutorial on verifying electrum wallet signature.
The procedure is same except Ledger live signed hashes uses SHA512.
Here now let’s see how to check hash / signature prior to installing the Ledger Live app?
How to verify checksum of Ledger live?
For each new release the sha512sum hashes for ledger live is published here: https://live.ledger.tools/lld-signatures
https://github.com/LedgerHQ/ledger-live-desktop#signed-hashes
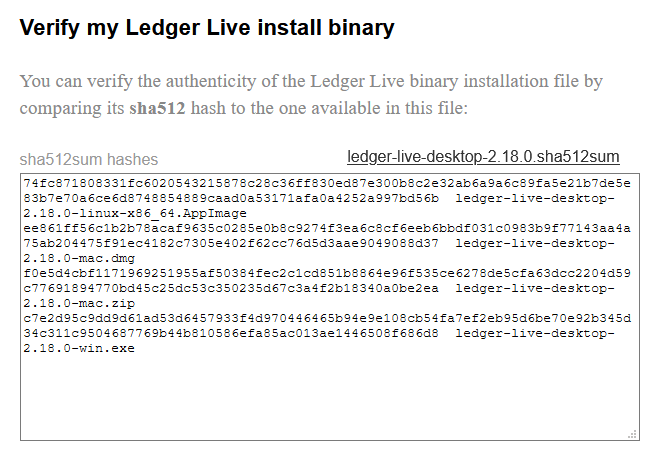
You can verify the authenticity of Ledger live installation by comparing its sha512 hash to the one available on the page.
This information is not available on the official download page of the website for a reason. The hash stored on the same server as binary doesn’t provide any security. If the server gets hacked both the file will be compromised.
Verifying hash of the installation package:
Download the latest version Ledger live app to your computer. Once downloaded do not install yet. Only install after successful verification.
Here is how you can verify the checksum on Windows, Linux and Mac.
- Windows:
Go to the folder where you have the download file. Press SHIFT + right click and open PowerShell window. Now enter the following command.
CertUtil -hashfile filename.exe sha512
Example:
CertUtil -hashfile ledger-live-desktop-2.18.0-win.exe sha512
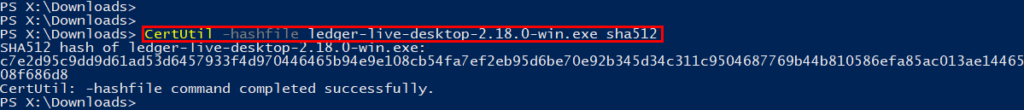
This will return the following result and depending on the version you are running the hash value will change.
SHA512 hash of ledger-live-desktop-2.18.0-win.exe: c7e2d95c9dd9d61ad53d6457933f4d970446465b94e9e108cb54fa7ef2eb95d6be70e92b345d34c311c9504687769b44b810586efa85ac013ae1446508f686d8
Copy this and compare its sha512 hash to the one available on this page: https://live.ledger.tools/lld-signatures
If it matches then you have a genuine copy. You can go ahead and install it
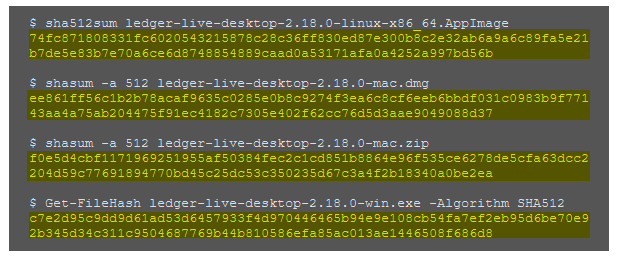
- Linux:
On Linux open Terminal window and enter the following code.
Sha512sum <path>/<filename>
Example:
sha256sum <path>/ledger-live-desktop-2.18.0-linux-x86_64.AppImage
- Mac:
On Mac open Terminal window and input the following line.
shasum -a 512 filename
Example:
shasum -a 512 ledger-live-desktop-2.18.0-mac.dmg
Once done with the sha512sum hashes verification you can proceed with the installation.
PGP signature verification?
PGP signatures are a great way to ensure file security and trust. But there is no reference to PGP signatures available on the download page of the ledger site or on the GitHub release.
Once they publish PGP signature we’ll update this article and explain how to verify PGP signature of Ledger Live. If you own Trezor device then here is how to verify PGP signature for Trezor suite.



Shift + Right Click pops up a menu, but Power Shell is not on it.
Since Ledger Live is the official desktop application from Ledger that acts as an interface with the Ledger Nano hardware wallet it is important to verify software. Excellent Guide.